AWS Hacking Workshop
About
AWS Hacking Workshop
Understanding Offensive Techniques in Amazon Web Services (AWS)
💻 Bring Your Laptop -Live Exploitation Exercises Included
Cloud environments have become the backbone of modern infrastructure, but misconfigurations and weak identity controls often expose them to attackers. In this hands-on workshop, we explore how adversaries gain access to AWS environments, move laterally, escalate privileges, and ultimately take control of cloud resources.
This workshop focuses on real-world offensive techniques used by attackers and red teamers to compromise AWS environments -and how these attacks actually happen in practice.
What You'll Learn & Practice:
01 -AWS Fundamentals for Attackers
Understand the core AWS architecture from an attacker’s perspective -including accounts, services, regions, networking, and the shared responsibility model. Learn how attackers map and understand AWS environments before launching attacks.
02 -AWS Identity & Access Management (IAM)
Explore how AWS identities work, including users, roles, policies, and permissions. Learn how attackers abuse misconfigured IAM policies, role assumptions, and credential leaks to gain deeper access into AWS environments.
03 -Initial Access Techniques in AWS
Discover how attackers obtain their first foothold in AWS environments. We will demonstrate real-world techniques such as credential exposure, access key abuse, metadata service exploitation, and misconfigured services.
04 -Post-Access Enumeration & Exploitation
Once inside an AWS account, attackers begin mapping the environment. Learn techniques for enumerating services, identifying sensitive resources, abusing misconfigurations, and extracting valuable data.
05 -Privilege Escalation in AWS Environments
Understand how attackers escalate privileges from low-level access to full administrative control. We will explore common IAM privilege escalation paths, role chaining, policy abuse, and service misconfigurations.
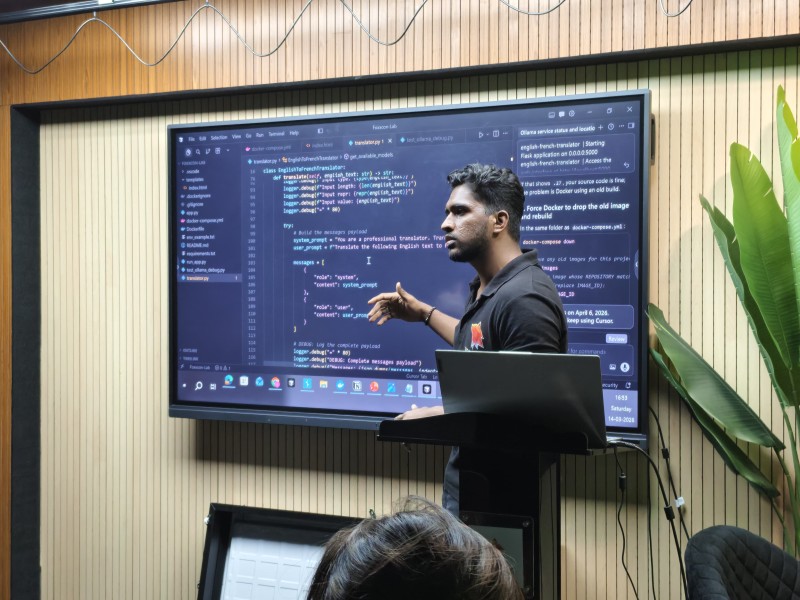
06 -Live Hands-On Attacks -Bring Your Laptop
This workshop is fully practical. You will perform real AWS attack scenarios in a controlled lab environment, including enumeration, exploitation, and privilege escalation techniques used by real attackers.
Come ready to hack -your laptop will be your primary tool throughout the workshop.
Ideal for:
Security professionals, penetration testers, red teamers, cloud engineers, and anyone interested in offensive cloud security.