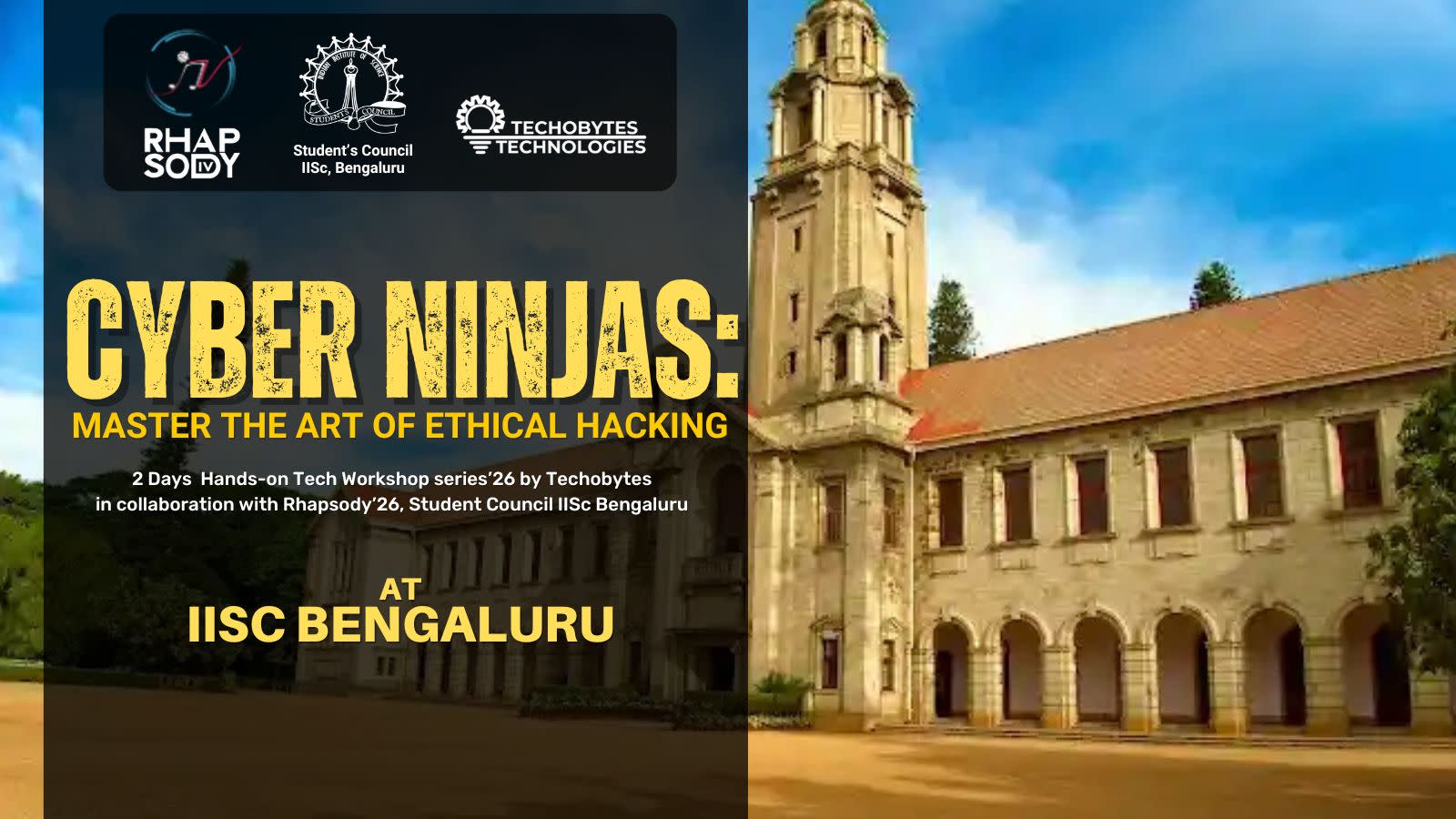
Cyber Security with Ethical Hacking | 2 Day Workshop at IISC Bengaluru
About
Advanced Tech Workshop 2026
Eligibility
Open to all!!
B.Tech, B.E., BCA, MCA, B.Sc IT, M.Sc IT, MBBS, MS, MD, Biomedical, Biotechnology, BBA, MBA, B.A., and hobbyists from all backgrounds
Session 1: Introduction to Ethical Hacking & Cyber Security
● Overview of ethical hacking
● Understanding the role of cybersecurity in protecting individuals and organizations
● Different types of hackers
● Scope and limitations of ethical hacking
Session 2: Footprinting and Reconnaissance
● Information gathering techniques
● Understanding OSINT
● WHOIS lookup
● Social engineering for reconnaissance
● Hands-on exercises and demonstrations
Session 3: Scanning and Enumeration
● Network scanning techniques
● TCP & UDP Scanning Background
● Port scanning
● Service enumeration
● Vulnerability Identification with Nmap
Session 4: Mobile Application Analysis
● Root detection and SSL pinning concepts
● Bypass root detection and ssl pinning in mobile apps
● Static analysis of android apps
● Android app dynamic analysis and attacks using burpsuite
Session 5: Vulnerability Assessment
● Importance of vulnerability assessment
● Tools for vulnerability scanning
● Common vulnerabilities and exposures (CVEs)
● Hands-On Exercise: Conducting a basic network scan and vulnerability assessment
Session 6: Exploitation and post-exploitation
● Malware & Exploits
● Metasploit framework
● Privilege escalation Techniques (Windows & Linux)
● Post-exploitation techniques
● Pivoting concept
Day 2: Advanced Penetration Testing Techniques Session 7: Web application attacks
● Burpsuite configuration and basics of web request and response
● Intro to web app bug bounty
● Offensive web application attacks
● SQL injection
● File upload vulnerabilities
● Web app business logic bypas
● Authentication attacks
● broken access controls in web apps
● HTML injection and Cross site scripting
● phishing user data via vulnerable web apps
● OWASP Top 10 vulnerabilities
● CSRF, XSS and SSRF
● Authentication & Access Control Vulnerabilities
● Hands-On Exercise: Exploiting a vulnerable web application
Session 8: Mobile Application Security
● Connecting Mobile Device to Burp Proxy
● Common mobile app vulnerabilities
● Basics of SSL Pinning
● Reverse engineering mobile apps
● Securing mobile applications
● Hands-On Exercise: Assessing the security of a mobile application
Session 9: Wireless Network Security
● Types of wireless networks
● Wi-Fi encryption protocols
● Wireless security threats
● Hands-On Exercise: Wireless network attacks
Session 10: CTF (Capture the Flag) Challenges for Students.
● Intro to CTF challenges and live CTF solving session
● Live demonstrations and hands-on exercises with CTF Labs
● CTF Lab setup
● CTF challenges for student batches
Session 11: Cybersecurity Best Practices
● Intro to SIEM and incident response
● Legal aspects of ethical hacking
● Continuous monitoring and improvement
● Building a career in ethical hacking
● Hands-On Exercise: Building a basic incident response plan
Additionally, topics like IoT hacking concepts, Software Defined Radio (SDR), etc., will be discussed with students. The workshop will be interactive and include practical exercises, demonstrations, and hands-on labs to engage the students and provide them with real-world experiences in ethical hacking and cybersecurity along with career guidance.